Devlog
First, the kaleidoscope
Beads, mirrors, and the gentle art of turning chaos into symmetry.
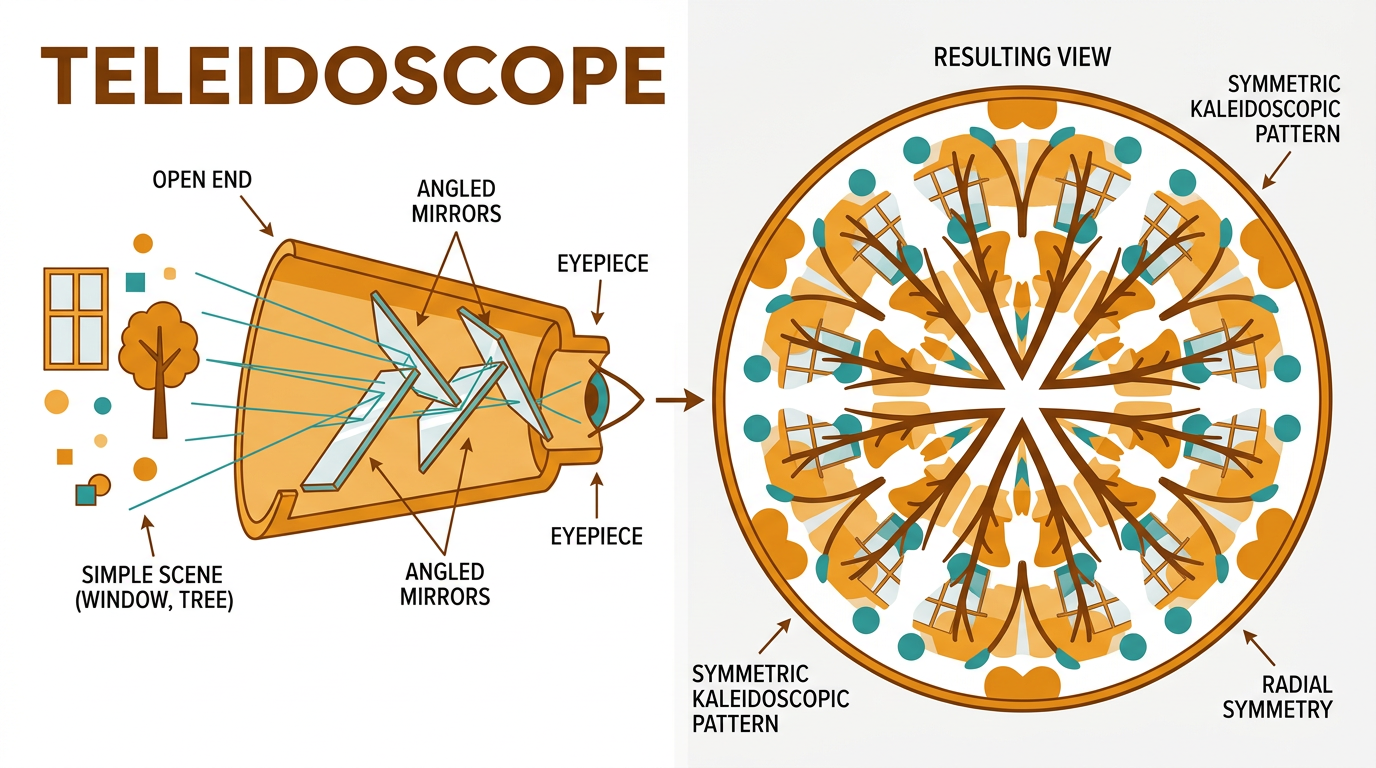
You’ve probably held a kaleidoscope: a tube, an eyepiece, and when you twist it, a storm of colored fragments tumbles into perfect radial symmetry. Triangles of glass or plastic bounce and settle; the mirrors inside multiply them into a pattern that feels both random and inevitable.
The magic is in the mirrors. Usually two or three, arranged in a triangle or a wedge. The angle between them decides how many “copies” of the scene you get—60° gives you sixfold symmetry, 45° gives you eight. The objects (beads, confetti, whatever’s in the “object cell” at the far end) are just the raw material. The mirrors are the engine. They take one messy input and produce a structured view.
Enter the teleidoscope
Now take away the object cell. No beads. No little chamber of tumbling bits. Just a tube with mirrors and a lens—and an open end you point at whatever’s in front of you.
That’s a teleidoscope. (From Greek tele “far” and eidos “form”—you’re seeing the “form of the distant,” i.e. the world you’re aimed at.) Point it at a window and the frame multiplies into a cathedral of light. Point it at a tree and the branches fold into a mandala. The world is the object. The mirrors turn it into a pattern. Same reality; completely different view.
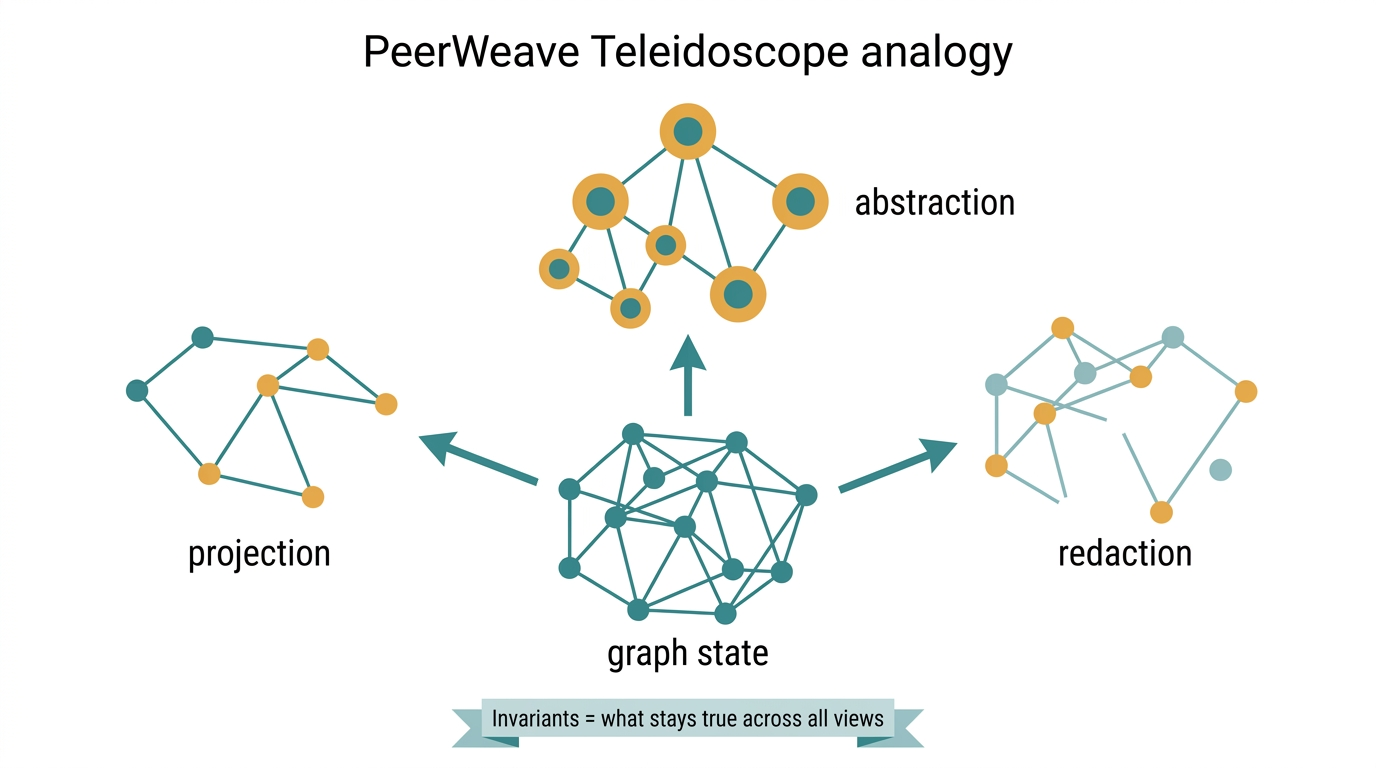
That’s the idea we stole for PeerWeave. Not the pretty pattern part—the one reality, many views part. Our “world” is a graph: code, agents, security boundaries, traces, commits. Our “mirrors” are transforms: projection, abstraction, redaction, temporalization. And the thing we care about isn’t just the view—it’s what stays true no matter which mirror you look through. We call those invariants.
Why name a subsystem after a toy?
PeerWeave already has a graph. Semantic nodes (files, functions, agents, ports, mirrors), a security knowledge graph (capabilities, trust zones, policies), and trace graphs (what an agent did, in what order). The problem isn’t “we need more graph.” The problem is: the same graph can be seen in wildly different ways depending on who’s looking and why.
- A security reviewer wants: “Only the bits that touch sensitive assets and publication boundaries.”
- An architect wants: “Modules and dependencies, not every single function.”
- An agent wants: “What did I do, in causal order, and what’s still true after I abstract away the noise?”
Same underlying state. Different “mirrors.” So we gave the formal layer a name that reminds us: we’re not building a single canonical view. We’re building a Teleidoscope—a way to point at the graph and twist the mirrors until the view you need appears, while still being able to ask “what stayed true?”
The formal kernel in plain language
Under the hood, the Teleidoscope Formal Kernel (we have a draft spec for the curious) is a small set of ideas that fit right into PeerWeave’s existing graph, security, and agent stack. No new language, no separate runtime—just a way to talk about graph state and transformations in a precise way.
Here’s the thesis in one sentence:
A PeerWeave graph state is a typed object. A mirror or lens is a typed transformation over that state. A transform chain is a composable path. An invariant is a property that’s preserved under a given class of transformations. And operationally, transforms run as graph rewrite rules with preservation contracts.
In other words:
- GraphObject — The “reality” the teleidoscope is pointed at. Your semantic graph at a commit, your security graph for a space, your trace graph for an agent run. Typed, identifiable, and reconstructible from real PeerWeave state.
- Transform — A mirror. It takes a graph in and produces a graph out. Projection (slice to a subset of node types), abstraction (collapse functions into modules), redaction (mask sensitive bits), temporalization (expand into time), causalization (derive cause from order). Each transform has a domain, a codomain, and a “loss mode”: lossless, controlled loss, or lossy.
- TransformPath — A chain of mirrors. “Projection, then redaction, then normalization.” Order often matters: abstract-then-redact can differ from redact-then-abstract. Paths are first-class so we can reason about equivalent chains and path-dependent invariants.
- Invariant — What stays true. “No path from SensitiveAsset to PublicArtifact without REDACTS.” “The dependency cycle still exists after we collapse functions into files.” “Retrieval still precedes proposal in the trace.” We check invariants on graphs and on whole paths; if an invariant is preserved under a transform, we know the view didn’t lie about that fact.
What you can actually do with it
The spec calls out three canonical use cases that make the metaphor concrete:
- Security publication validation. You have a private semantic/security graph. You run a path: projection (only publication-relevant bits) → redaction (sensitive nodes masked or removed) → normalization. You check invariants: no path from sensitive to public without redaction, no leaked capability scope. The result is a publishable graph plus a validation report. Same idea as “point the teleidoscope at the graph and turn until the view is safe to share.”
- Agent trace compression. You have a raw syscall/event trace. You run: temporalization → abstraction → causalization. You check: retrieval precedes proposal, access checks preserved. The result is a semantic behavioral trace—what the agent “did” in human-meaningful terms, without losing the invariants that matter for auditing.
- Architecture skeleton persistence. You have a semantic graph across commits. You collapse functions into files, files into modules, then normalize. You check: does the dependency cycle persist? Do cross-module boundaries change? You get a structural change report that survives refactors.
In every case, the graph is the world. The transforms are the mirrors. The invariants are the things we refuse to lose when we change the view.
The twist: structure vs. artifact
The kernel’s real value isn’t “we have transforms.” It’s that we can distinguish structure from representation artifact. Is that cycle in the graph “really” there, or did we introduce it by picking a weird projection? Is that path from SensitiveAsset to PublicArtifact still closed after redaction, or did we accidentally leave a hole? Invariants answer that. They’re the contract: “under this class of transforms, this property holds.” If it holds, the structure is real. If it breaks, the mirror (or the transform chain) is telling us something we need to fix.
PeerWeave already does invariant-style reasoning in the security layer. The Teleidoscope kernel generalizes that: same idea, but for semantics, traces, publication, and agent behavior. One formalism, one engine, one UI contract (select graph → apply transforms → inspect preserved/lost structure → compare paths → save as lens). And because everything is capability-bound and trace-recorded, agents and humans both get to use the same mirrors without bypassing authority.
So what?
Most platforms stop at “we drew your graph.” PeerWeave is aiming for “we can transform your graph in typed, auditable ways and tell you what stayed true.” That’s the step change. Not another visualization—a reasoning engine over graph state, with mirrors you can twist and invariants you can trust.
If that sounds like a teleidoscope—one world, many views, and a way to know what’s still real when the pattern shifts—good. That’s the idea. Now we just have to build the tube and point it at the mesh.
For the full formal story—primitive transforms, invariant kinds, capability model, trace events, and API sketch—see the Teleidoscope Formal Kernel v0.1 spec. This post is the “why it’s named that and why you might care” version. The spec is the “here’s what we’re actually implementing” version.